- Shorten your response time
- Optimize your existing tools and infrastructure
- View and manage incidents from a single windowpane
SECURITY ORCHESTRATION, AUTOMATION, AND RESPONSE
Better your response time.
Security, orchestration, automation, and response is a tool that collects information across security technologies and, with predetermined criteria, acts upon that information.
SOAR, in short, supports and standardizes response and security operations by automating human and security tasks.
Four SOAR pillars as defined by Gartner:
- Worfklow and collaboration
- Ticket and case management
- Orchestration and automation
- Threat intelligence management
A well-rounded SOAR tool offers to improve your security operations in the following ways:
- No more silos – Unite tools in your technology stack, allow for better use of your existing tools via orchestration and automated tasks.
- One solution – Endless possibilities in orchestrating your security team’s processes from day-to-day management to response and case management via a single platform.
Why SOAR
Your business and security team may benefit from security orchestration, automation, and response if…
- Your security team experiences burnout cycles
- You have trouble maintaining consistent, quality talent
- Your team is overloaded with alerts and your team may be required to manually address each one
- Your team’s response time takes days or weeks (mean time to respond is poor)
- Your team hops from tool to tool in order to gather relevant data for analysis, and you don’t have a centralized case management tool
- Your team lacks standardized processes, or they are becoming too complex to carry out effectively
- Your business is facing more advanced threat actors
Visibility – Gain full visibility across your existing stack.
Automation – Automate manual tasks.
Unification – Unify your existing tools and get more out of your current investments.
Communication – Communicate with business stakeholders or key players in the response process.
Workload – Reduce noise and the amount of alerts your team puts eyes on, allowing your team to focus on other necessary projects.
Management – Manage incidents from beginning to end, centralize your case management as well as your vulnerabilities and remediation processes.
Integral – Improve your security posture and mean time to respond.
Standardization – Standardize your incident processes and procedures.
Collaboration – Auto-route incidents to specific team members and boost collaboration amongst your team members.
Valuation – Raise your SOC’s value and show it with KPI dashboarding and reporting capabilities.
Operational – Operate more efficiently.
Scalability – Scale your response consistently as you grow.
SOAR Platforms / Vendors
While SOAR technology can provide many benefits to your security team, there are quite a few platforms or vendors your business can choose to purchase, such as those listed below. (Please note: This is not a complete list.)
(It’s essential to keep in mind that your team must have the skill and talent necessary to maintain the platform and continue to evolve its use as you will just be purchasing the software and some pre-built / out-of-the-box features.)
Anomali ThreatStream
Cyberbit SOC3D
Cyware Virtual Cyber Fusion Center
D3 Security
DFLabs IncMan SOAR
EclecticIQ
Exabeam IncidentResponder
FireEye Helix
Fortinet (CyberSponse) FortiSOAR
IBM Security (Co3 Systems)
LogicHub SOAR+
Micro Focus (ATAR Labs)
Palo Alto Networks Cortex XSOAR (Demisto)
Rapid7 InsightConnect
ServiceNow
Siemplify
Splunk Phantom
Swimlane
ThreatConnect
ThreatQuotient
SIEM vs SOAR vs MDR
COMPARE & CONTRAST
Can SOAR take the place of SIEM and MDR or vice versa? Let’s take a look at the role each of these tools plays in response.
SIEM
The heart of your security ecosystem, SIEM aggregates all your data and is the basis for all investigations. Depending on your SIEM, your team may also have the ability to categorize that data and analyze incidents or events thereafter, looking for patterns and anomalous activity. The SIEM issues alerts to analysts for follow up.
But on its own, SIEM is unable to isolate a host after an incident (MDR) or automate security tasks following an incident (SOAR), although some SIEMs on the market have SOAR-like capabilities.
Then, of course, is the classic argument MDR vs SIEM. (And the closely related argument – MDR vs SIEM vs MSSP as a webinar and MDR vs SIEM vs MSSP as an article.)
SOAR
SOAR platforms help your team better its operations by automating manual tasks and by orchestrating your standardized response to an incident. SOAR acts upon the data in your SIEM, and across your existing tools via integrations, and even enriches your alerts. While SIEM aggregates your data, SOAR allows your analysts to collaborate on investigations and view an incident from a centralized point.
And like SIEM, SOAR is not a “set-it-and-forget-it” tool. Those looking to grow their SOC with a SOAR tool will need resources to maintain the technology and realize its potential over time. At its core, SOAR integrates your team’s tools and streamlines your processes.
And like MDR, SOAR can help your team perform triage activities and detect advanced attacks on your network.
MDR
Endpoint Detection and Response tools, and managed services around those tools, assist with detection and response activities, including isolating an infected host among other quarantine options. EDR, when layered over the SIEM for extra visibility, can act upon the data in your SIEM and your SIEM is able to provide additional information including log data for further investigation and forensics-work. By adding SOAR as a layer over EDR, host isolation can be in effect automatically once certain playbook criteria are met.
SIEM and EDR are essential parts of the security ecosystem that can be optimized with a SOAR product.
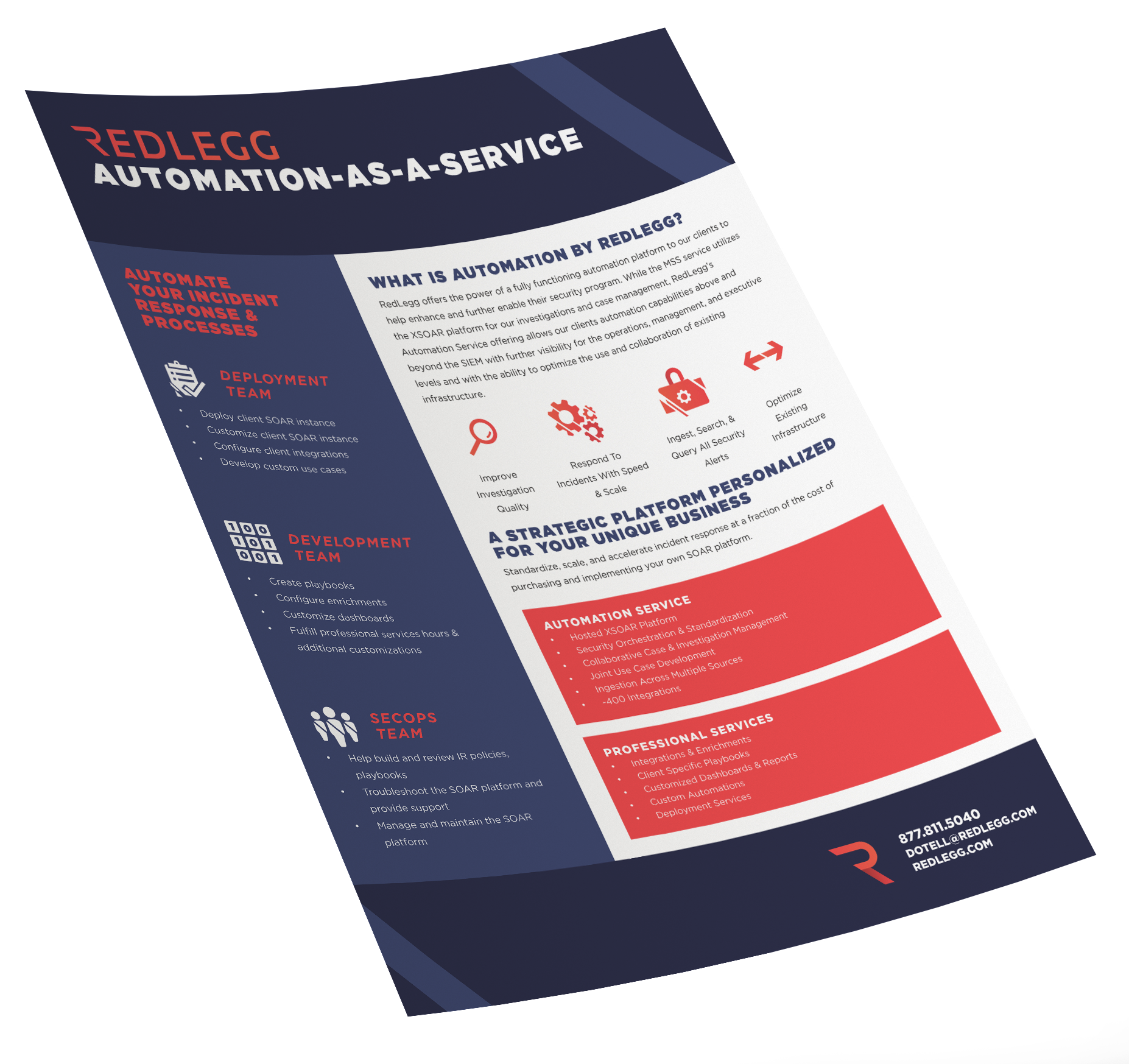
SOAR-as-a-Service
The Trouble With SOAR Platforms
Like we stated earlier in this article, SOAR platforms are never a “set-it-and-forget-it” or “out-of-the-box” investment.
To get your SOAR platform up and running, you’ll need an Automation Developer, someone to manage the platform, team members to write and create response policies and procedures, and investigation, analysis, and incident response experts on staff.
With an already existing shortage of talent in the cybersecurity community, growing your SOC may seem like a daunting or even infeasible challenge (even without considering the costs of purchasing your own SOAR platform).
In short, SOAR requires true security expertise across many tools and functions.
Enter SOAR-as-a-Service.
Benefits Of SOAR-as-a-Service
Much like the capabilities of SOC-as-a-Service, SOAR-as-a-Service can cover the talent shortage while helping you standardize, scale, and accelerate your incident response and your security program.
If you already own a SOAR platform, get it up and running with provided Automation Developers or get experts to help you deploy your instance then standardize your unique processes and procedures.
If you’re looking to get started in SOAR, consider a solution like RedLegg’s SOAR-as-a-Service which offers a hosted Palo Alto Networks Cortex XSOAR option, all at a fraction of the cost of purchasing and implementing your own SOAR platform.
All the benefits of SOAR with the consistent talent you need.
Learn more about RedLegg's Automation-as-a-Service (SOAR).
Benefits
See how an Automation service can help your team & your business.
DOWNLOAD NOW